Windows Defender ransomware protection blocks unauthorized access to critical folders via controlled folder access, keeping essential files safe from malware encryption without disrupting trusted applications.
Ransomware threatens data integrity by encrypting files and demanding payment. Windows Defender provides an effective built-in defense layer. This feature requires manual configuration for optimal activation. Therefore, understanding precise procedures becomes key to maximum protection.
Important note: Ransomware protection options remain inactive by default in Windows Defender. This prevents conflicts with third-party security solutions that may experience false positives.
Understanding Ransomware Threats and Defense Mechanisms
Ransomware represents malware that locks data access through encryption. Attackers then demand payment for decryption keys. However, payment does not guarantee file recovery. Some advanced variants use cryptoviral extortion techniques that prove difficult to trace.
Furthermore, modern ransomware attacks target critical infrastructure and supply chains. Therefore, layered protection becomes an urgent necessity. Windows Defender offers controlled folder access as a preventive solution. This feature restricts application access to sensitive folders based on reputation and trust.
No guarantee exists that ransom payment restores file access. Proactive prevention through security configuration proves more effective than reactive response after attacks occur.
Activating Ransomware Protection in Windows Defender
The controlled folder access feature works by verifying applications against a trusted list. Unknown applications get blocked when attempting to modify files in protected folders. The activation process requires several simple configuration steps.
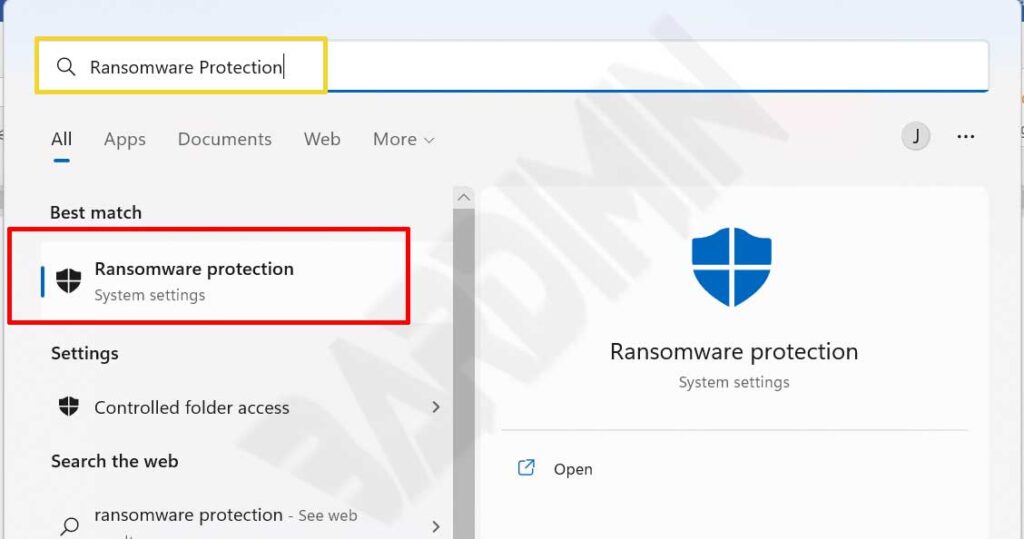
- Open the Windows search menu by pressing Windows + S on your keyboard.
- Type “ransomware protection” in the search field, then press Enter.
- The system will open the Ransomware protection page in Windows Security.
- Locate the “Controlled folder access” section on the settings panel.
- Toggle the switch to On position to enable ransomware protecion.
- Confirm any UAC prompt that appears to grant administrative privileges.
After activation, the system monitors access to default folders like Documents, Pictures, and Downloads. Windows also protects important system folders automatically. Users can add custom folders according to specific needs.
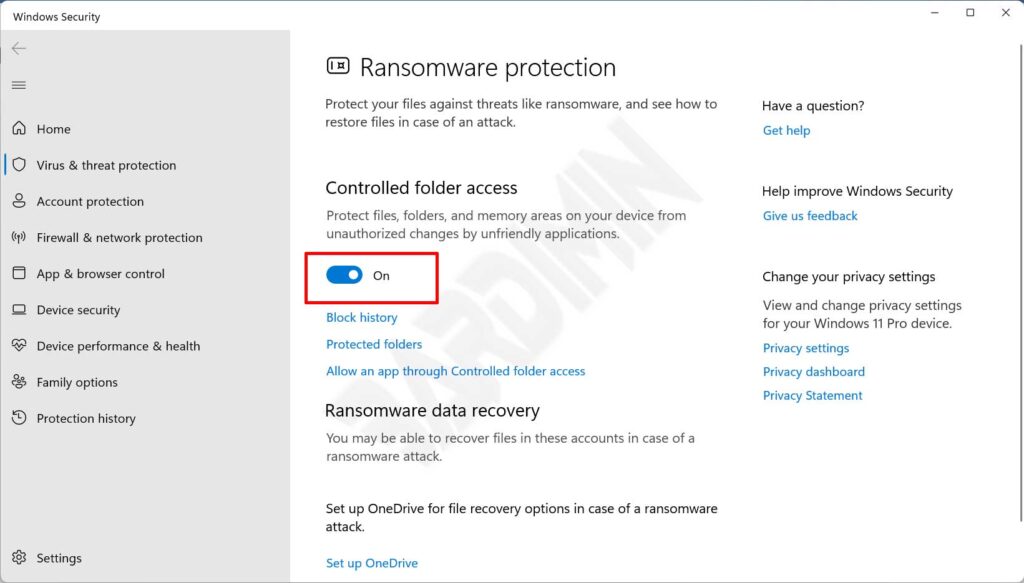
Activation verification: Ensure the toggle status shows blue and displays “On”. If the toggle returns to Off position, check group policies or third-party antivirus that might cause conflicts.
Managing Application Permissions in Controlled Folder Access
Activating ransomware protection can block legitimate applications not yet registered. Therefore, configuring application permissions becomes a crucial step. Windows Defender provides two methods for managing application access.
Method 1: Using Block History
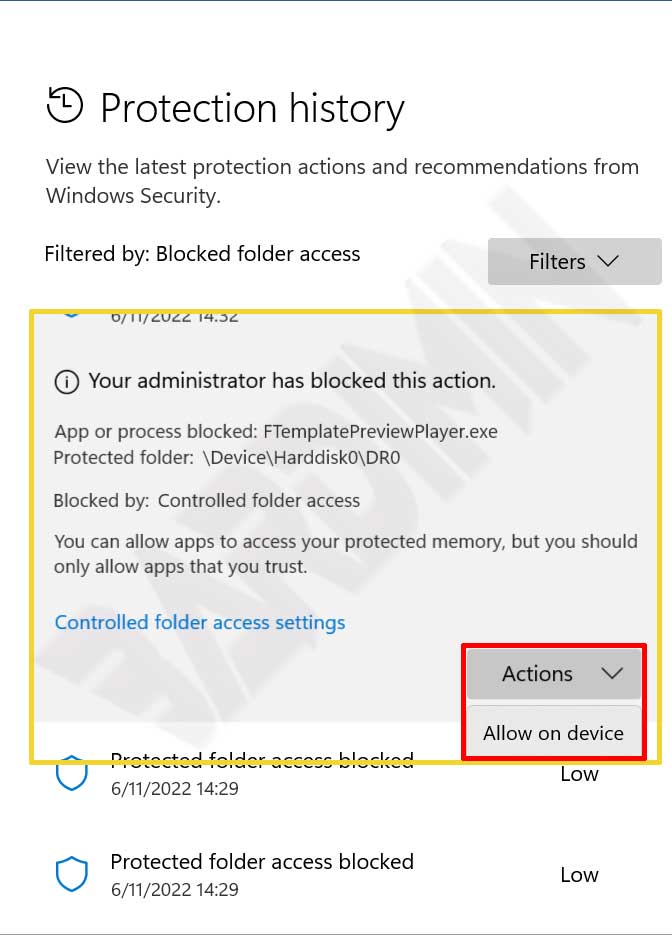
Block History records all applications blocked when attempting to access protected folders. This method works ideally for quickly permitting recently blocked applications.
- Click the “Block history” button on the ransomware protection page.
- A list of blocked applications appears with event timestamps.
- Select the history entry you want to manage to expand details.
- Click the “Actions” dropdown beside the selected entry.
- Choose “Allow on device” option to grant permanent permission.
- Confirm your selection in the security dialog that appears.
Method 2: Adding Applications Manually
This method allows adding trusted applications before they get blocked. This step suits proactive deployment in work environments.
- Click the link “Allow an app through Controlled folder access”.
- Select the “Add an allowed app” button on the appearing panel.
- The system offers two options: “Recently blocked apps” or “Browse all apps”.
- Choose “Recently blocked apps” to view newly blocked applications.
- Click the plus (+) icon beside the application to grant access permission.
- Or select “Browse all apps” to search for executable files manually.
- Navigate to the application installation directory, select the .exe file, then click Open.
- Confirm the application addition in the User Account Control dialog.
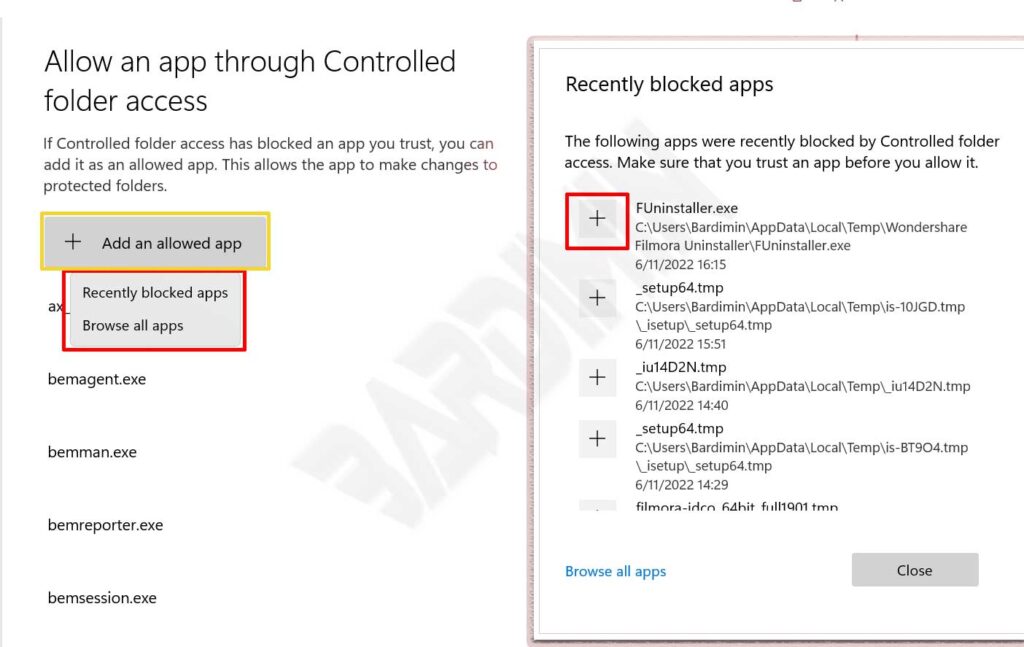
Professional tip: Script engines like PowerShell do not become trusted automatically. Add them manually if needed for specific workflows. Always verify exe file integrity before granting permissions.
Best Practices for Optimizing Ransomware Protection
Basic configuration alone does not provide maximum protection. Implement the following practices to enhance your system security effectiveness.
- Enable real-time protection: Ensure real-time scanning always runs for instant threat detection.
- Update virus definitions: Regular updates ensure protection recognizes newest ransomware variants.
- Create external backups: Store important file backups on media separate from your main system.
- Use multi-factor authentication: Additional authentication layers restrict unauthorized account access.
- Educate users: Security awareness training reduces infection risks from phishing emails.
- Monitor event logs: Check Event Viewer regularly to detect suspicious activity patterns.
However, avoid adding network share paths as protected folders. Use direct local paths for correct configuration. Subfolders automatically get included in protection when parent folders get added.
Controlled folder access blocks file changes by untrusted applications. This system uses behavioral analysis and application reputation for security decisions.
Microsoft Security Documentation
Monitoring and Evaluating Protection Effectiveness
Windows Defender provides monitoring tools for evaluating ransomware protection performance. Event Viewer records controlled folder access activity with specific event codes.
- Event ID 1123: Records folder access blocking by untrusted applications.
- Event ID 1124: Records audit activity for security policy evaluation.
- Event ID 5007: Records ransomware protection setting changes by users.
- Event ID 1001: Records ransomware threat detection and remediation events.
Microsoft Defender portal also provides centralized reporting for enterprise environments. Advanced hunting features enable custom queries for incident investigation. Therefore, security teams can respond to threats more quickly and accurately.
Troubleshooting: If legitimate applications keep getting blocked, check executable paths and add installation folders to the trusted list. Restart your system after major configuration changes.
Windows Defender ransomware protection delivers solid defense with minimal configuration. However, optimal security requires a layered approach. Combine built-in features with security best practices for maximum results. Protect your digital assets starting today with proper activation and configuration.
