GNS3 is widely used to simulate, configure, test, and troubleshoot real and virtual networks.
GNS3 allows you to manage topologies of any size, from those with multiple devices hosted on your laptop to those with multiple devices spread across multiple servers or even hosted in the cloud.
GNS3, which at first could only emulate Cisco hardware using a program called Dynamips, has developed and can emulate various network hardware, including virtual switches from Cisco, ASA from Cisco, Brocade vRouters, Cumulus Linux switches, Docker instances, HPE VSR, various Linux appliances, and more.
GNS3 supports not only Cisco hardware. However, GNS3 now supports a variety of additional open source and commercial suppliers. Networking technologies with SDN, NFV, Linux, and Docker allow you to test interoperability among different manufacturers and even try out unusual settings.
Advantages of Using GNS3
- Free software
- Open Source software
- No monthly or annual license fees
- There is no limit to the number of supported devices (the only limit is your hardware: CPU and memory)
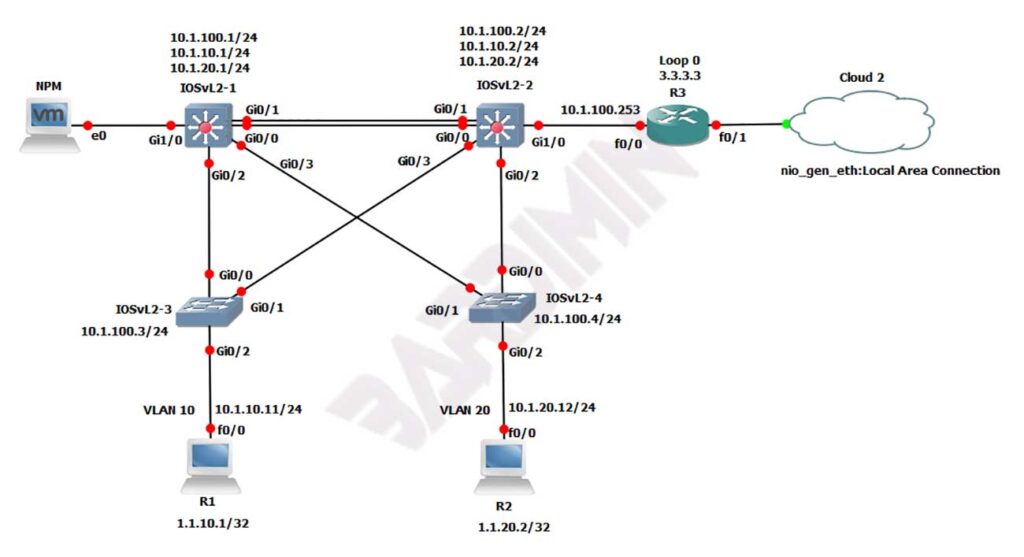
- Supports multiple switching options ( Etherswitch NM-ESW16 module, Layer 2 IOU/IOL image, IOSvL2 VIRL):
- Supports all VIRL images (IOSv, IOSvL2, IOS-XRv, CSR1000v, NX-OSv, ASAv)
- Supports multi-vendor environments
- Can be run with or without a hypervisor
- Supports both free and paid hypervisors (VirtualBox, Vmware workstation, Vmware player, ESXi, Fusion)
- Downloadable, free, preconfigured, and optimized tools are available to simplify deployment
- Native support for Linux with no additional virtualization software
- Software from multiple vendors is freely available
- Large and active community (800,000+ members)
Disadvantages of Using GNS3
- The Cisco image must be provided by the user (download it from Cisco.com, purchase a VIRL license, or copy it from a physical device).
- Not a standalone package, but requires local software (GUI) installation.
- GNS3 can be affected by your PC’s settings and restrictions because of local installation (firewall and security settings, corporate laptop policies, etc).
Download GNS3
You must first login before you can download.
Mac GN3 v 2.2.33.1
