What are VLANs?
Virtual Local Area Network or better known as “VLAN” is a subnetwork capable of grouping devices on a local area network (LAN) that are physically separated into one logical network.
VLANs arise because the complexity of the existing network has exceeded the capacity of the LAN. Initially, LANs connected a group of computers with servers using cables that were in the same physical location. However, in the current development, LAN is also connected via the internet network and also through wireless devices.
A large organization, of course, needs a solution that allows the network to grow in the future. VLANs, with their virtual nature, allow organizations to grow in terms of size, flexibility, and complexity because VLANs are not limited by device location.
VLANs make it easy for network administrators to group devices connected to a network. VLAN membership can be configured via software so that network topology design can be simplified. Without a VLAN, creating a group of devices would require extra effort, cost, and time to build the infrastructure.
Using VLANs helps improve overall network performance by grouping the devices that communicate the most. VLANs also provide security on larger networks by allowing a higher level of control over which devices have access to one another. VLANs are flexible because they are based on logical, not physical connections.
VLAN Type
port based
Port-based VLANs group local area networks by port. Each port can be configured manually as a member of a specific VLAN.
In one port, several VLANs can be configured in “trunk” mode. To find out a port as a member of a VLAN which cannot be physically seen on the “switch”, but must look at the configuration on the switch.
MAC based
MAC-based VLAN group’s network and VLAN membership are based on the MAC address of each device. Each switch has a MAC Address table for each device along with the assigned VLAN group.
Protocol based
Protocol-based VLANs handle traffic based on the protocol. The switch will separate or forward the traffic based on the traffic protocol.
Because VLANs can work at layer 2 (OSI) then the use of protocols (IP and IP Extended) as the basis for VLAN membership can be done.
VLANs can also work on layer 3 protocols, so the subnet addresses can be used as the basis for determining VLAN membership.
By using the 802.1x protocol, VLAN membership can also be determined based on user or device authentication.
VLAN Range
VLAN range table
| VLANs | description |
| VLAN 0 , VLAN 4095 | Backup, which cannot be viewed or used. |
| VLAN 1 | Default VLAN of the switch. Cannot be deleted, but can be used. |
| VLAN 2-1001 | Normal range of VLANs. Can be created, edited, and deleted. |
| VLAN 1002-1005 | Default VLAN used by Cisco. |
| VLAN 1006-4094 | Extended VLAN range |
How VLANs work
VLANs are identified by numbers. The usable range for VLAN IDs is 0-4095.
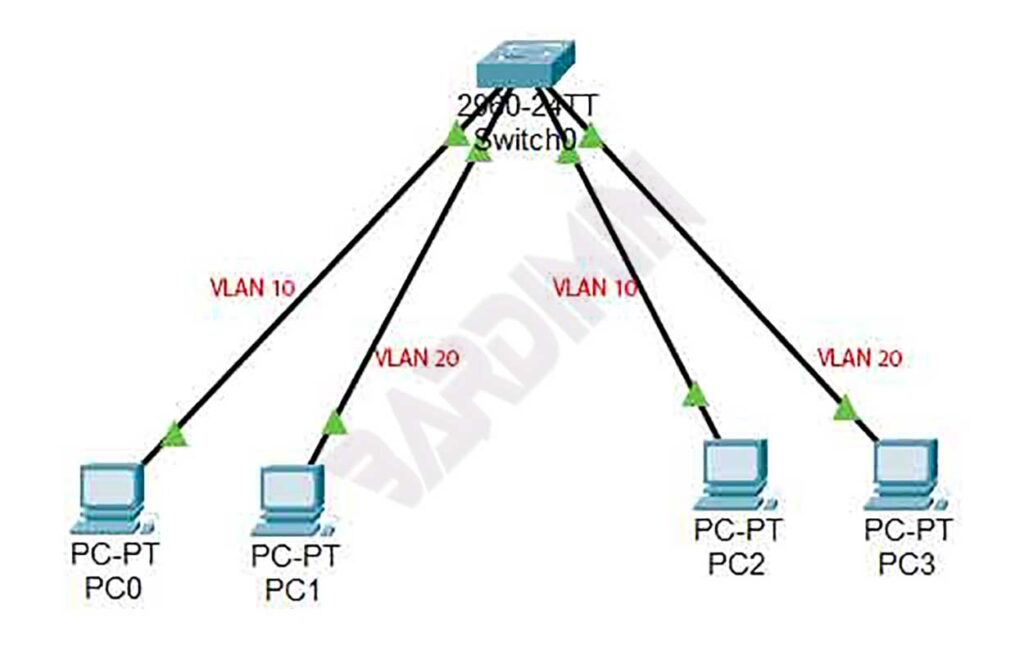
One port on the switch can be assigned one or more VLANs that allow dividing into logical groups.
Data communication on the switch occurs only on devices connected to ports with the same VLAN ID.
A network will consist of several switches because of the limited number of ports on a switch. To communicate between switches, the ports connected to other switches must be configured. The configuration on that port must allow all created VLANs to pass through that port in “trunk” mode. This configuration is carried out on each port that connects to other switches.
